Anatomy of a Ransomware Attack

Insights from portfolio company HYAS
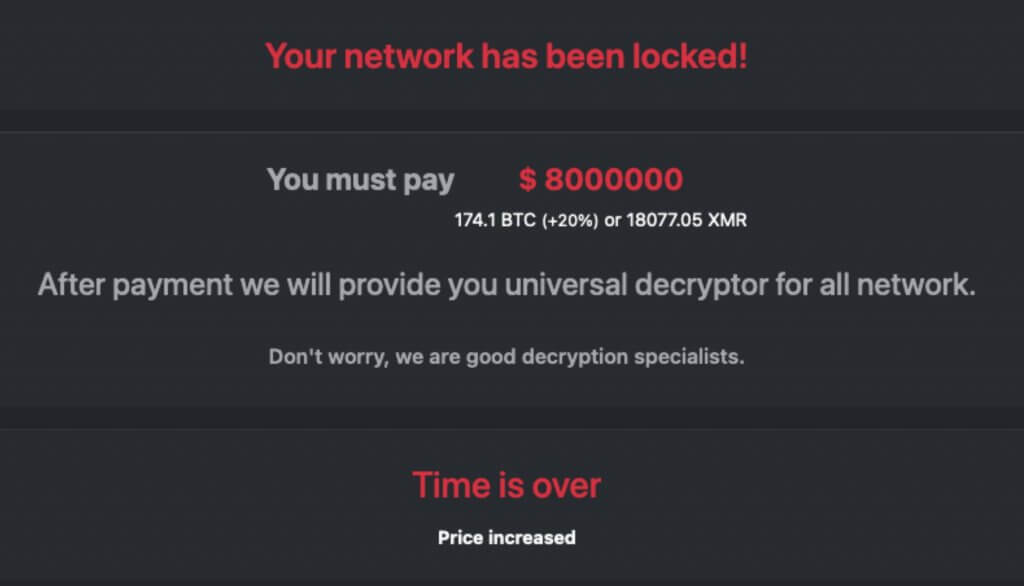
In recent years, ransomware has evolved from targeting individual computers to locking the files of entire enterprises or public institutions and infrastructure, and demanding exorbitant ransoms. Victims often have little choice but to pay, for fear of losing mission critical data or services. In fact, according to Ransomware Threat Report 2021, the average ransom paid by victim organizations in Europe, the US and Canada has almost tripled, from $115,123 in 2019 to $312,493 in 2020.
In addition to costly ransom payments, cyberattacks also affect consumer perception when sensitive data is being compromised. A Forbes Insight report found that 46% of organizations had suffered damage to their reputations and brand value as a result of a data breach – a reputation risk often overlooked when assessing the impacts of ransomware attacks.
How can attacks be prevented? As incidents such as the recent Colonial Pipeline attack make global headlines, portfolio company HYAS, a leading authority on cybersecurity, is often asked whether they could have detected and stopped such threat.
As always, the answer to that question is complicated. However, HYAS has valuable insights to share in their recent blog, “The Anatomy of a Ransomware Attack”. This piece describes the various steps in a typical ransomware attack, provides a number of key recommendations, and suggests where HYAS would be able to provide critical help.
Headquartered in Victoria, Canada, the company provides the industry’s first security solution that integrates into an organization’s existing security technology stack to proactively detect and mitigate cyber risks before attacks happen. The technology also identifies the infrastructure used, which can lead to the identities of the individuals behind the attacks. Threat and fraud response teams use HYAS to hunt, find, and identify adversary infrastructure while enterprises can proactively block both known and not-yet-launched phishing and ransomware attacks at the network layer.
I found these insights valuable and I know you will enjoy them as well.
Terry Matthews
Chairman
Wesley Clover
